Ad Networks offer affiliate programs that allow Affiliates to generate income. These affiliates are given an Affiliate ID that stores a cookie in a user’s browser for a specified period of time. If the user makes a sale/conversion before the cookie expires, the affiliate receives a commission for that sale/conversion.
What makes this approach unique is that it does not technically distribute any malicious content. If a user engaged with the page containing the iFrame on the compromised website, they simply transferred a network’s affiliate cookie to the user’s browser.
iFrame: It is used to add HTML code inside another HTML code. Generally, this technology is used to place ads on websites. Where advertisers are given a section on the website to place their creative codes.
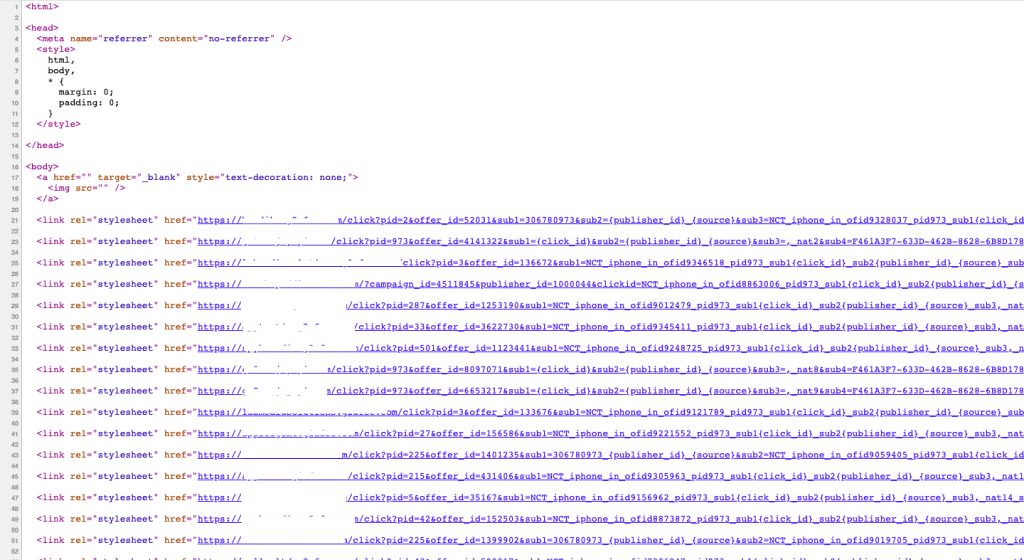
Here is an example of a publisher using Iframe pixel to stuff cookies on the user browser and generating fraud conversions.
<html>
<head>
<meta name=”referrer” content=”no-referrer” />
<style>
html,
body,
* {
margin: 0;
padding: 0;
}
</style>
</head>
<body>
<a href=”” target=”_blank” style=”text-decoration: none;”>
<img src=”” />
</a>
<link rel=”stylesheet” href=”https://trk.netowrk.com/click?pid=0000&offer_id=00000&sub1=&sub2=26&sub3=xyz&sub4=gaid&sub5=app-id&sub6=radom_id” />
</body>
When users visit a web page with a hidden iFrame like this, their browser loads all the content whether the user can see it or not. This includes affiliate cookies, which are then stored in the browser.
Some networks will inject up to 20 different hidden affiliate iFrames on a single page to maximize the opportunities. These invisible iFrames are known to slow page load times and can lead to negative user experience, but are otherwise harmless to users.
If the user makes a conversion before the injected iFrame cookie expires, network will receive a commission for the purchase.
By compromising more websites and distributing their injected Affiliate iFrames exposure is maximized as is the number of commissions generated for these black hat marketers clearly showing that unprotected websites are a resource valuable for bad actors.
To mitigate the risk of serving unwanted affiliate cookies or reducing site performance, website owners can closely monitor changes to their website files by using an integrity monitoring service. This service will make it easy to spot any suspicious or compromised activity.
What We Are Doing To Stop This Kind Of Fraud?
In Trackier we have created a shield to block any click coming from publisher tracking URL which seems to be the centre for image/ Iframe pixel for cookie stuffing.
Our dedicated server keeps a watch 24*7 for this kind of traffic and keep blocking it, which makes you safe from paying fraud conversion to your affiliate and managing disrupted CR with advertisers.
The above image is a sample as to what cookie stuffing fraud looks like. With cookie stuffing, you’re committing a crime against another affiliate or the advertisers who is paying commissions on sales that would have happened anyway.